The contemporary digital landscape is defined by an escalating arms race between application developers and automated threat actors. As business-critical applications become increasingly open to the global internet, the risk of Distributed Denial of Service (DDoS) attacks, particularly at the HTTP application layer, has shifted from a rare possibility to an inevitability. While infrastructure-level protection services like AWS Shield provide a robust baseline for Layers 3 and 4, the vast majority of modern malicious events manifest at Layer 7, where they overload specific application endpoints with an unusually high volume of HTTP requests. These attacks are not merely volumetric; they are increasingly sophisticated, leveraging IP rotation, TLS stack variation, and targeted behavioral patterns to bypass traditional security perimeters. Within this context, AWS Web Application Firewall (WAF) rate-based rules have emerged as an invaluable mechanism for automated mitigation, allowing organizations to distinguish between legitimate traffic bursts and malicious flood events with surgical precision.
The Technical Mechanism of Rate-Based Rule Aggregation
The fundamental efficacy of a rate-based rule lies in its ability to monitor the request volume from specific source identifiers within a defined temporal window. The core mechanism involves the AWS WAF infrastructure detecting the identifier—typically a client IP address—and aggregating the number of incoming requests over a sliding five-minute interval. This process relies on a “bucket” system where the WAF maintains a count of requests per identifier for every five-minute period. If the number of requests exceeds a user-defined threshold, the WAF initiates a mitigation action, such as blocking the identifier or counting the requests for logging and alerting purposes.
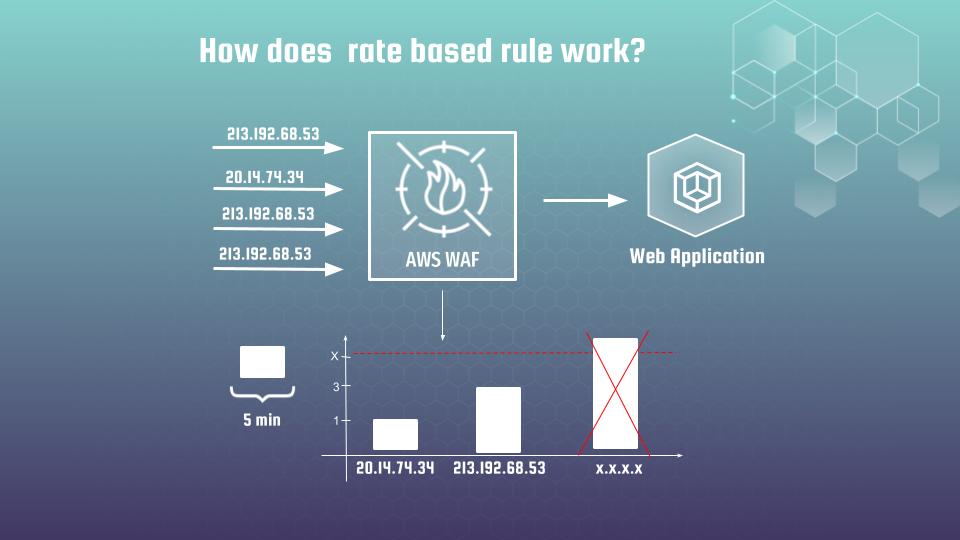
The mitigation action remains active as long as the request volume for that specific identifier stays above the threshold within the trailing five-minute window. Once the rate of requests falls below the set limit, the block is automatically lifted, and the identifier is once again allowed to access the application. This automated lifecycle is a significant improvement over static IP blacklisting, which often fails to account for the dynamic nature of botnets and the potential for temporary IP hijacking. In 2025, the granularity of these rules has been further enhanced, allowing for evaluation windows to be customized down to one minute, thereby providing security teams with the ability to react more rapidly to sudden, high-intensity spikes.
The Strategic Architecture of the Rate Rule Funnel
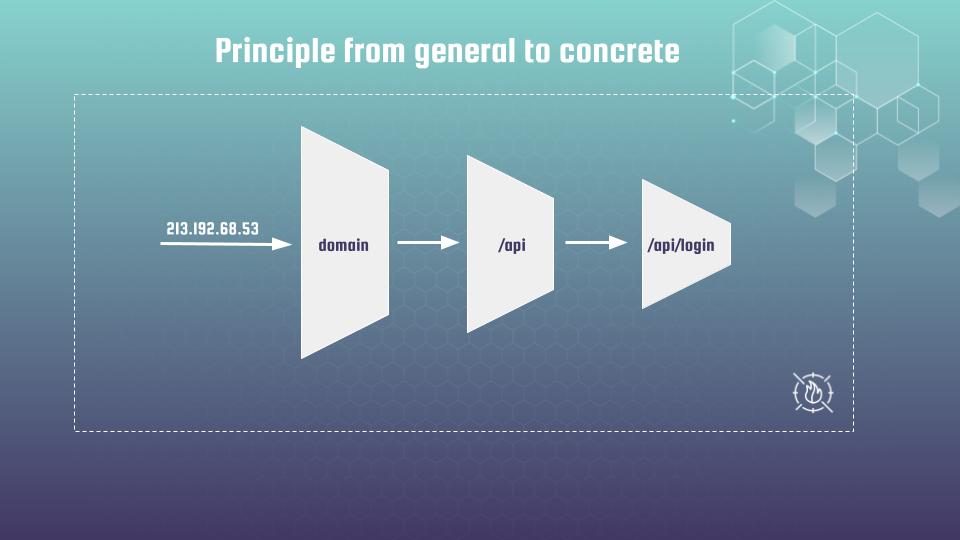
A single, global rate limit is rarely sufficient for a modern, multi-functional web application. Professional security practitioners advocate for the “funnel principle,” a hierarchical strategy that applies rate limits with increasing granularity from the general domain level down to concrete, high-risk URLs. This principle ensures that the widest variety of unwanted traffic is caught at the highest level of the infrastructure, while legitimate users retain access to the broader application even if a specific, high-intensity functional group is under attack.
General Perimeter Defense (Level 1: The Blanket Rule)
At the widest part of the funnel, a “blanket” rule is implemented to protect the entire application or domain. This rule calculates the aggregate number of requests for every unique client IP across the total namespace of the application. The threshold for this rule is typically set high enough to accommodate the most active human users—such as internal power users or heavy searchers—while preventing any single source from overwhelming the server.
The primary objective of the blanket rule is to mitigate rudimentary scripts and unrefined volumetric attacks. Because it applies to every path, it serves as the first line of defense, ensuring that no single entity can degrade the performance of the entire site. In advanced configurations, this level may also utilize JA4 TLS fingerprinting to detect bursts of traffic that share a technical profile, even if they are distributed across multiple rotating IP addresses.
Functional and Category Grouping (Level 2: The Mid-Tier Funnel)
As traffic moves deeper into the application, the funnel narrows to distinguish between critical groups of functionality. In a typical e-commerce or content platform, these groups may include API endpoints, product landing pages, or category search results. Modern scrapers often exhibit a behavior where they scan category pages first—a process known as surface exploration—before diving deeper into individual product pages. By establishing a mid-tier rule for paths such as /cars/* or /api/*, security teams can block aggressive scrapers as they attempt to map the site’s contents.
This level of the funnel is particularly effective for managing the performance of specific backend services. For instance, a search API may be significantly more computationally expensive to serve than a static landing page. Applying a more restrictive rate limit to the /api/search namespace prevents a single crawler from exhausting the database connection pool while allowing normal browsing traffic to continue unaffected.
Granular Endpoint Protection (Level 3: The Concrete Rule)
The tip of the funnel targets the most sensitive and vulnerable addresses in the application namespace. Classical examples include login forms, password reset endpoints, and authorization APIs. Because these endpoints are prime targets for brute-force attacks and credential stuffing, they require the most restrictive thresholds.
A concrete rule for /api/login might have a threshold as low as 10 to 20 requests per five minutes. At this level of granularity, the WAF is essentially enforcing a security policy that is specific to the business logic of the endpoint. The success of this granular approach relies heavily on maintaining a clean URL structure. When application addresses are organized logically, it becomes far easier to apply precise regular expressions and scope-down statements to target specific behaviors without impacting adjacent services.
| unnel Level | Sample Target | Primary Goal | Typical Threshold |
| Global/JA4 | Entire Domain | Early DDoS & tool detection | 2,000+ |
| URL Category | /cars/*,/electronics/* | Block aggressive scrapers | 500 – 1,000 |
| Landing Page | /cars/opel | Detect targeted automation | 100 – 300 |
| API Endpoint | /api/login, /api/search | Protect expensive DB/Auth | 10 – 50 |
The Imperative for Precise Rate Rules
The necessity for precision in rate limiting is driven by the fact that not all malicious traffic manifests as a global spike [Image 2]. Sophisticated scrapers and botnets are increasingly adept at flying under the radar of blanket rules by targeting specific, high-value pages with lower-volume, highly distributed requests.
Behavioral Dynamics of Automated Scrapers
Crawlers typically follow a logical progression: they begin with surface exploration, hitting category pages to identify new content, and only later descend into deeper, more resource-intensive pages. If an organization relies solely on a high-threshold blanket rule, these scrapers can effectively harvest data at the category level indefinitely, as their per-IP request volume remains below the global limit.
Furthermore, many bots only target certain business-valuable pages, such as price comparison tools or stock availability checks. Precise rate rules allow for the detection of these targeted patterns. By monitoring the request rate specifically for high-value endpoints, the WAF can identify anomalous activity that is lost in the “noise” of general site traffic.
Strategic Advantage of JA4 TLS Fingerprinting
One of the most significant challenges in modern perimeter defense is IP rotation. Modern botnets can rotate through thousands of innocent-looking residential IP addresses, each sending only one or two requests per minute. To a traditional IP-based rate rule, this traffic looks legitimate. JA4 fingerprinting addresses this by looking at the “shape” of the TLS ClientHello packet—the technical profile of the software stack initiating the connection.
While an attacker can easily rotate IPs, they rarely rotate their underlying TLS configuration or HTTP library. JA4 creates a unique signature based on the proposed cipher suites, extensions, and TLS versions. By using JA4 as an aggregation key in a rate-based rule, the WAF can catch a scanner that is rotating thousands of IPs because all those requests share the exact same (and often highly specific) TLS fingerprint. This technical signal allows the WAF to treat the entire botnet as a single entity for the purposes of rate limiting, effectively neutralizing the advantage of IP rotation.
Quantitative Analytics: Calculating Thresholds with Amazon Athena
Determining the appropriate threshold for a rate-based rule is a technical challenge that must be approached with empirical data. Setting a threshold too low results in false positives that degrade the user experience, while setting it too high leaves the application vulnerable to exploitation. The standard methodology for threshold calculation involves analyzing Application Load Balancer (ALB) access logs using Amazon Athena.
The calculation process begins with the delivery of ALB/CloudFront access logs to an Amazon S3 bucket. These logs provide a granular record of every request, including the client IP, the request time, the targeted domain, and the URI path. Amazon Athena then serves as the serverless query engine, allowing security teams to execute standard SQL against these raw log files to identify historical traffic patterns.
Before querying, a proper table schema must be established in Athena. Practitioners often use partition projection to improve query performance and reduce costs, particularly when dealing with massive datasets generated by high-traffic applications.
The Core Threshold Query
To find the maximum number of requests any single client IP has sent within a 5-minute window, a query must bucketize the request times into 300-second intervals. This is achieved by using the floor function on the Unix timestamp of each request.
The following SQL logic illustrates the calculation of request counts per IP in 5-minute buckets :
To find the maximum number of requests any single client IP has sent within a 5-minute window, a query must bucketize the request times into 300-second intervals. This is achieved by using the floor function on the Unix timestamp of each request.
The following SQL logic illustrates the calculation of request counts per IP in 5-minute buckets :
SELECT
from_unixtime(floor(to_unixtime(from_iso8601_timestamp(time)) / 300) * 300) AS time_bucket,
client_ip,
COUNT(client_ip) AS request_count
FROM alb_logs
WHERE domain_name = 'your-application-subdomain.com'
AND parse_datetime(time, 'yyyy-MM-dd''T''HH:mm:ss.SSSSSS''Z')
BETWEEN parse_datetime('2025-01-01-00:00:00', 'yyyy-MM-dd-HH:mm:ss')
AND parse_datetime('2025-01-01-23:59:59', 'yyyy-MM-dd-HH:mm:ss')
GROUP BY 1, 2
HAVING COUNT(client_ip) > 1
ORDER BY request_count DESC;Analyzing Results and Applying Buffers
xecuting this query reveals the peak request volume of the most active legitimate users. Security analysts should look for the highest values returned in the request_count column. For instance, if the most active legitimate user (excluding known internal crawlers or bots) makes 80 requests in a 5-minute period, setting the threshold at 100 provides a comfortable buffer while still catching any significant deviations.
Generally, it is recommended to add a 10% to 20% buffer to the identified maximum threshold to account for natural variations in traffic and legitimate application growth. This analysis should be performed regularly, as the introduction of new application features or changes in user behavior can drastically alter the baseline traffic profile.
Infrastructure as Code: Terraform Implementation of Rate Rules
Automating the deployment of AWS WAF configurations is a cornerstone of modern DevOps and SecOps practices. Terraform allows for the declarative definition of Web ACLs and rate-based rules, ensuring consistency across development, staging, and production environments.
A robust Terraform module for WAF rate rules relies on a well-structured variables.tf file. By using a list of objects, developers can dynamically generate multiple rate rules for different URL patterns without duplicating resource blocks.
variable "rate_url_rules" {
type = list(object({
name = string
priority = number
limit = number
action = string
search_string = string
positional_constraint = string
metric_name = string
}))
description = "A list of URI-specific rate rules to apply to the WAF."
}Dynamic Rule Generation in the Web ACL
The aws_wafv2_web_acl resource uses a dynamic block to iterate over the defined rate_url_rules. Each iteration creates a rate_based_statement that applies a scope_down_statement to target the specific URI path.
resource "aws_wafv2_web_acl" "main_acl" {
name = "production-web-acl"
scope = "CLOUDFRONT"
default_action {
allow {}
}
dynamic "rule" {
for_each = var.rate_url_rules
content {
name = rule.value.name
priority = rule.value.priority
action {
dynamic "block" {
for_each = rule.value.action == "block"? :
content {}
}
dynamic "count" {
for_each = rule.value.action == "count"? :
content {}
}
}
statement {
rate_based_statement {
limit = rule.value.limit
aggregate_key_type = "IP"
scope_down_statement {
byte_match_statement {
search_string = rule.value.search_string
field_to_match {
uri_path {}
}
text_transformation {
priority = 1
type = "NONE"
}
positional_constraint = rule.value.positional_constraint
}
}
}
}
visibility_config {
cloudwatch_metrics_enabled = true
metric_name = rule.value.metric_name
sampled_requests_enabled = true
}
}
}
}This configuration allows for granular control over evaluation actions—setting rules to block in production while using count for testing new thresholds. Furthermore, the visibility_config ensures that every rule match is logged to CloudWatch, providing the data necessary for future tuning and incident response.
With the introduction of JA4 support, Terraform configurations must now accommodate CUSTOM_KEYS for request aggregation. A JA4-based rate rule defines the fingerprint as the primary identifier and often includes a scope-down statement to limit the rule’s application to traffic identified as potential bot activity. For concrete examples, please, have a look here.
Verification and False Positive Mitigation
No security control is infallible, and the risk of blocking a legitimate customer is a persistent concern in WAF management. Verification workflows must be established to differentiate between sophisticated attackers and heavy legitimate users who happen to trigger a rate limit.
When a rate rule triggers a block, the initial investigation should center on the identity of the blocked IP. Security teams can use Athena to identify the exact IPs being blocked by a specific rule and then correlate that data with application-level logs.
The investigation should answer several key questions :
- User Identification: Does the blocked IP belong to a registered customer? Checking the application database for activity associated with that IP can provide immediate context.
- Registration History: How old is the user account? An account created years ago that suddenly exhibits high activity is likely a “good” user whose traffic pattern has changed, whereas a newly created account performing high-volume searches is more likely a bot.
- URI Journey: What sequence of URLs was the client visiting? A human journey—login -> browse -> search -> view item—differs significantly from a bot journey—search -> search -> search -> search.
In addition to internal logs, external reputation services can provide context on blocked IPs. Services like AbuseIP maintain real-time blacklists (RBLs) that track IPs associated with spam, malware, and known botnets. If a blocked IP appears on multiple reputable blacklists, the block is highly likely to be justified. Conversely, if an IP belongs to a major residential ISP and has no negative reputation history, it should be investigated as a potential false positive.
| Indicator | Legitimate User Profile | Malicious Actor Profile |
| Account Age | Months/Years | Days/Minutes |
| IP Reputation | Clean (Residential/Mobile) | Flagged (Hosting/Proxy/VPN) |
| URI Patterns | Logical navigation flow | Repetitive, high-volume endpoint hits |
| Headers | Consistent, standard Browser UA | Weird, mismatched, or default SDK UAs |
| TLS Signature | Standard (Chrome/Safari/Firefox) | Custom or outdated libraries (Go-http/Python) |
Advanced WAF Features and Strategic Maintenance
The efficacy of AWS WAF is not static; it requires continuous tuning and the adoption of advanced managed features to stay ahead of evolving threats.
While custom rate rules provide granular control, AWS Managed Rules offer broad protection against known attack patterns. The AWSManagedRulesBotControlRuleSet is a critical addition to any Web ACL. This rule set uses advanced heuristics to classify traffic into categories such as verified_bot (e.g., Googlebot), unverified_bot, and non_browser_user_agent.
Integrating these managed rules at the top of the funnel allows for the early elimination of noise traffic. For example, the AmazonIpReputationList can be prioritized to block known malicious sources before they are even evaluated by the custom rate rules, thereby saving WCU (Web ACL Capacity Units) and reducing processing latency.
Strategic Log Analysis for Optimization
Beyond security, WAF and ALB logs are a goldmine for application performance optimization. A rate analysis might reveal that a specific frontend component is making redundant API calls, or that an external service is stuck in a redirection loop that generates thousands of unnecessary requests.
Regularly reviewing top-performing IPs and URI paths with Athena can highlight these inefficiencies. If a specific IP is making 1,000 requests per 5 minutes to a static asset that should be cached at the CDN level, it indicates a misconfiguration in the application’s caching headers rather than a security threat. Resolving these issues not only improves site speed for all users but also reduces the compute load on the backend infrastructure.
Long-Term Perimeter Governance
A professional WAF deployment should be treated as a living system. Maintenance activities should include :
- Quarterly Threshold Reviews: Recalculating thresholds using Athena every 3-6 months to ensure they align with legitimate application growth.
- Drift Detection: Ensuring that the WAF configuration in AWS matches the Terraform source of truth, preventing “hotfixes” made in the console from becoming permanent without proper documentation.
- Alarm Sensitivity Tuning: Adjusting CloudWatch alarm thresholds for rate-rule matches to ensure the security team is notified of genuine attacks without being overwhelmed by minor traffic spikes.
- Security Lifecycle Integration: Incorporating WAF rule updates into the software development life cycle (SDLC). When a new high-value endpoint is deployed, a corresponding rate rule should be part of the infrastructure-as-code pull request.
The transition from a basic security posture to a mature, data-driven defense requires a commitment to quantitative analysis and automated infrastructure management. By leveraging the funnel principle, utilizing the precision of JA4 fingerprinting, and anchoring thresholds in empirical log data, organizations can build a perimeter that is both resilient to attack and transparent to legitimate users. The integration of these strategies ensures that the AWS WAF remains not just a reactive firewall, but a strategic asset in the application’s overall architecture and performance strategy.
f you are interested in more information and hands-on practice regarding Advanced Architectural Strategies for AWS WAF, feel free to check out my courses:
- DevSecOps on AWS: Defend Against LLM Scrapers & Bot Traffic
- How to secure web application with AWS WAF and CloudWatch
Thank you for your attention.
Best regards!
